The Oji Group undertakes business activities with a strong sense of ethics set forth in the Oji Group Corporate Code of Conduct, and implements appropriate risk management practices. In response to the rapid expansion of the areas where we operate businesses, we will reinforce our risk management structure globally to ensure business continuity and the steady development of our businesses.
Under the development and supervision by the Board of Directors, the Oji Group has established Group Risk Management Regulations and works to manage risks in the flow described below.
The Directors and Corporate officers of Oji Holdings are responsible for reporting risks in the businesses and divisions under their control to the Group Management Meeting, and important risks are also reported to the Board of Directors.
The Oji Holdings Board of Directors reviews the effectiveness of the risk management process annually.

The Oji Group's risk management system is structured as shown in the diagram below and operates separately from the Audit & Supervisory Board and the Internal Audit Department.
The Audit & Supervisory Board and the Internal Audit Department also audit the status of risk management.

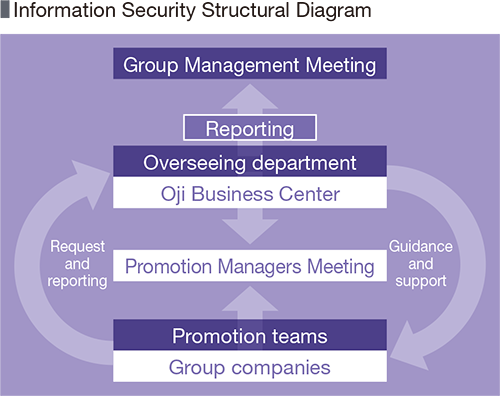
The Oji Group positions information obtained through its business activities as important assets. We have enacted Information Systems Usage and Risk Management Regulations to respond promptly to changes in the ever-sophisticating IT environment, and have established all group system to prepare for cyber threats such as unauthorized across prevention and disasters. The Oji Business Center, as a department that oversees our information system risk management, inspects the information system risks across the Group, and maintains, manages and improves IT security. In addition, it regularly provides educational activities and information on the latest risk trends it has captured to employees using company newsletters, and conducts targeted email training for employees to deal with phishing e-mails that are becoming more sophisticated every day. In FY2021, we revised regulations to respond to changes in work styles, such as the spread of cloud computing and teleworking in times of COVID-19. We will work to make sure that these measures will take hold and further strengthen our efforts to improve IT security from a global perspective.
The Oji Group categorizes major risks that may have a material effect on its financial position, etc. into three groups: risks of long-term issues, risks associated with its management strategies, and risks arising from the execution of business. At the same time, the Group takes the following measures to address each risk group.
Icons to the right represent material issues
| Type of risk | Content of risk | Main countermeasures against risks | |
|---|---|---|---|
| Risks of long-term issues |
Climate change |
The Task Force on Climate-related Financial Disclosures (TCFD), see | |
|
Pandemic
|
Risk of health damage to employees or temporary suspension of operations being caused by the global spread of infection similar to COVID-19 |
|
|
| Risks associated with our management strategies |
Structural changes in demand arising from development of innovation
|
Risk of structural changes in demand arising from the movement towards digital transformation (DX), which brings significant changes to people’s lifestyles and business activities. |
|
|
Fluctuations in demand |
Risk of decline in demand for products arising from domestic business fluctuations and a continuing decline in population |
|
|
|
Fluctuations in global market conditions
|
Risk associated with procurement prices of raw materials and fuels which are influenced mainly by fluctuations in demand, countries’ changes to their trade policies, and wars Risk of sales prices of pulp being influenced by global market prices |
|
|
|
Overseas business |
Geopolitical risks, including war, political or social instability, decelerating economic growth, revisions to laws, regulations, and tax systems, destabilizing financial conditions, human rights issues, etc. taking place in overseas markets where the Group operates |
|
|
| Risks arising from execution of business |
Occurrence of disasters, etc.
|
Risk of production bases and supply chain in and outside Japan being affected by natural disaster Risk of fire, occupational accident, environmental accident and other unexpected circumstance occurring |
|
|
Laws, regulations, and other rules
|
Risk of not being able to comply with laws and regulations of various countries, and their revisions and amendments |
|
|
|
Litigations and other actions
|
Risk of being a party to litigations, disputes, or other legal proceedings in the course of business |
|
|
|
Product liability |
Risk of damages based on product liability being claimed |
|
|
|
Exchange rate fluctuations
|
Risk of fluctuations in exchange rates in product sales, raw material purchases and other transactions using various currencies |
|
|
|
Information leakage |
Risk of confidential information being leaked due to willful conduct including external cyberattacks or negligence |
|
|